How it works
When deciding to grant access to employees to your MRI OnLocation account, there are several rules or policies you can use to ensure your OnLocation account has the same access rules as your other applications. For example, you may want the employee to set a password that contains a minimum of 6 or 8 characters and you may want the password to include upper case, lower case, and symbols.
In some instances you may not want your employees to have to set a separate password in OnLocation, preferring them instead to be logged in once they log into their PC automatically. This can be set using single sign-on with SAML.
Manage employee access settings
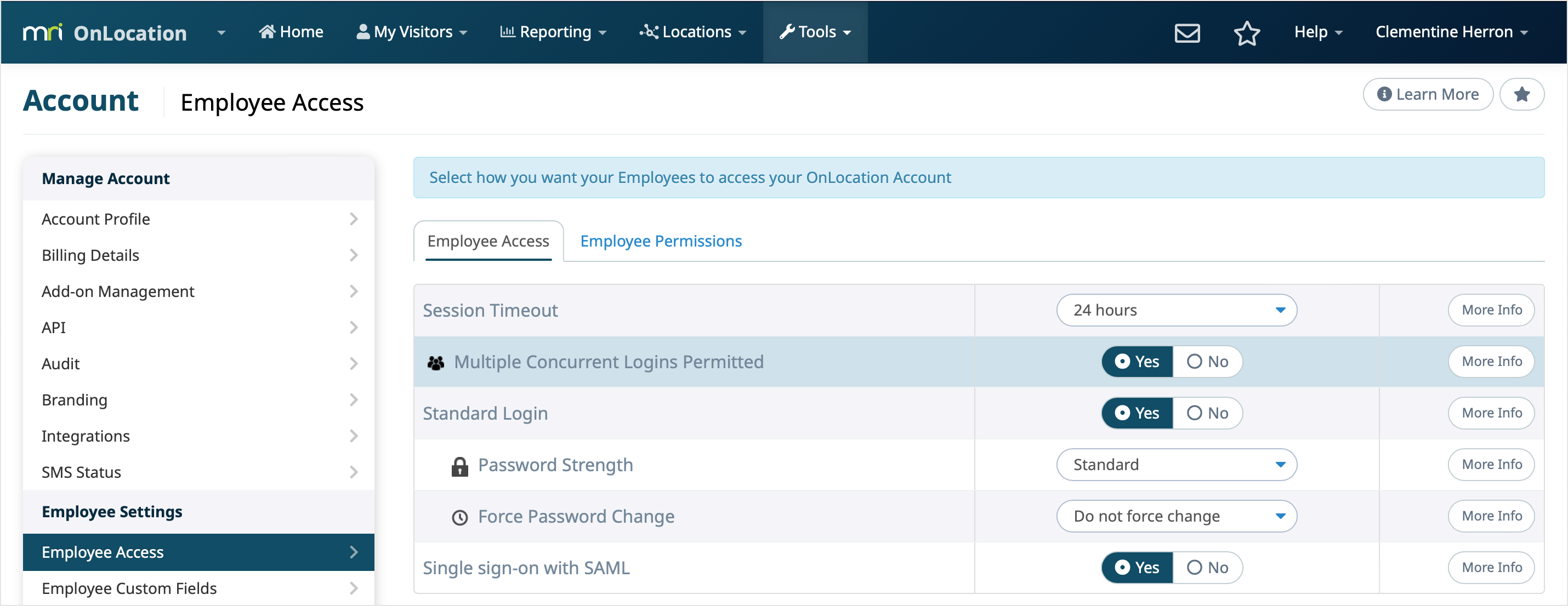
To make changes to the employee access settings:
- Go to Tools > Account.
- Select Employee Access from the left-hand menu.
These settings will be automatically saved as soon as they are set and will be applied from that point forward.
Both Account Owners and IT Support users have access to the employee access settings. This is because employee access can often require some network settings or are required to meet online security levels which are managed by the IT team.
Standard login
This is the user authentication that OnLocation provides by default with every account. In practice, user profiles are created manually by the Administrator or automatically via a sync with Active Directory.
Once their profile is created, the Administrator grants access to the employee by sending them an activation link. To do this:
- Go to Locations, then select the location from the drop-down list.
- Select Employees.
- Select the checkbox next to the employee's name
- Scroll down to the Run Action menu, then select Send Login Permission Email.
- Click Run Action.
The employee will be automatically sent an email from OnLocation to the email address in their profile, the email includes a unique link for the employee. The employee selects the link which takes them to the OnLocation Login screen where they are verified and create their own password.
The user then logs into your OnLocation account using their email address and password. OnLocation takes care of authenticating the user and allowing them access to your OnLocation account.
Multiple concurrent logins
When multiple concurrent logins permitted is enabled, a user can sign in from as many different machines and browsers with the same account as they like. If this is disabled, a user can only sign into one machine at a time meaning that multiple people cannot effectively use one account. This gives greater security around identifying users who make changes, sign people in, and pre-register visitors in OnLocation.
Password strength
Best practice and security auditors recommend that to meet the minimum for compliance, with standards like OWASP, HIPAA, and Sarbanes-Oxley, passwords should:
- Be a minimum of six, preferably eight, characters in length
- Be a combination of uppercase and lowercase letters
- Mixed with numbers and symbols (!, @, #, $, for example)
- Not contain personal information, such as the names of spouses or family members (including pets!) or any information that an attacker could easily derive from a user
OnLocation provides three password strength options:
- Simple: minimum of 6 characters
- Standard: (the default) minimum of 6 characters; combination of uppercase and lowercase letters
- Complex: (recommended) minimum of 8 characters; combination of uppercase and lowercase letters with at least one number and one symbol (!, @, #, $, for example)
Force password change
Best practice and security auditors recommend that to meet the minimum for compliance, with standards like OWASP, HIPAA, and Sarbanes-Oxley, passwords should be changed every 45 to 90 days and should be different every time.
The default setting is 'Do not force change'.
Single sign-on with SAML
Single sign-on is a mechanism that allows you to authenticate users in your systems and subsequently tell OnLocation that the user has been authenticated. The user is then allowed to access OnLocation without being prompted to enter separate login credentials.
You have complete control over your users and they don't necessarily need a separate password to log in to your OnLocation. Instead, when users visit your OnLocation and attempt to log in, they are seamlessly redirected to your SAML server for authentication. Once authenticated, users are redirected back to your OnLocation and automatically logged in.
The only user data that needs to be contained in OnLocation is the user's email address or an external ID that you define. To learn more about single sign-on, view this article.